
Article Summary
- This article provides a crucial guide for users on how to protect themselves when interacting with smart contracts in the DeFi and NFT ecosystems.
- It explains that a smart contract is just a piece of code, and like any code, it can have bugs or malicious backdoors that put user funds at risk.
- The guide breaks down the most common smart contract risks, including re-entrancy attacks, rug pulls (malicious code), and unlimited token approvals.
- It provides a checklist of actionable steps users can take to protect themselves, such as researching the project, checking for audits, using a dedicated "burner" wallet, and revoking token approvals.
In DeFi, you skip the bank and interact with software. That sounds clean until you remember one detail: software breaks, and people lie. When you connect a wallet to a dApp, you let code touch your funds. If the code is weak or the app is malicious, you can lose everything.
Most users start in a crypto exchange and that is fine.
Exchanges like Bitunix handle custody and some security controls for you, which can reduce certain on-chain risks. But the moment you move on-chain to invest in DeFi, you switch roles. You become the risk team, the compliance team, and the person who clicks confirm.
This guide is not about learning to code. It's about learning to be a defensive user. We will cover the biggest risks you face when interacting with smart contracts and provide a practical checklist to help you protect your assets.
What is Smart Contract Risk?
Smart contract risk is the chance that the code you interact with does something you did not expect, or that someone exploits it to take funds. Smart contracts are often immutable after deployment, so a bug can live on-chain for a long time. Some projects use upgrade mechanisms, but upgrades introduce a different risk, including that admin keys and governance decisions can change behavior after you deposit.
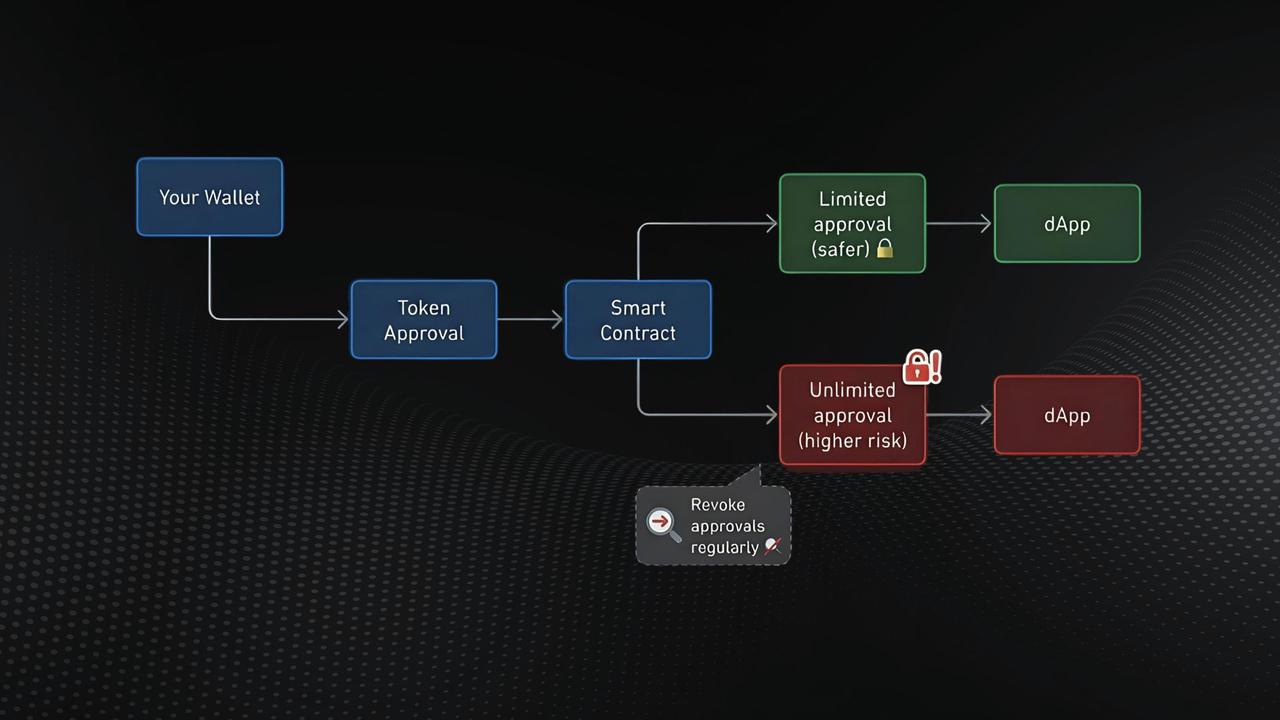
Think of it like handing your car keys to a valet. You expect parking. But you just handed over the ability to move the car. On-chain permissions work the same way. When you approve a contract, you give it the ability to move tokens that belong to you, and that permission can stick around long after you forget it.
A DeFi wallet is powerful and risky because it gives you direct access to dApps, and those dApps can access your assets once you approve them. The losses in 2025 show how often attackers target users. CertiK tracked $2.47B lost in H1 2025, with wallet compromise alone at about $1.71B (34 incidents) and phishing at about $410.7M (132 incidents). Chainalysis estimated $3.4B stolen in 2025, and TRM Labs reported $2.87B stolen across nearly 150 hacks, driven heavily by a single mega-breach.
The Most Common Risks
Most on-chain disasters fall into a few repeating patterns. You will see different branding and different chains, but the mechanics stay familiar. Below are three risks that matter for almost every DeFi user and NFT collector.
Re-entrancy Attacks (The Classic Hack)
A re-entrancy bug happens when a contract sends funds before it updates its internal balance. An attacker calls the withdraw function, receives funds, and then re-enters the same function again before the contract finishes updating state.
The DAO hack in June 2016 is the classic re-entrancy cautionary tale. An attacker drained about 3.6 million ETH, roughly a third of the 11.5 million ETH raised, by repeatedly triggering a withdrawal path before the contract updated balances, and the funds sat in a child contract with a built-in waiting period. The fallout led to Ethereum’s July 20, 2016, hard fork at block 1,920,000, which moved roughly 12 million ETH into a recovery contract and ultimately split the network into Ethereum and Ethereum Classic.
Rug Pulls (Malicious Code)
Sometimes nothing is buggy. It is designed to steal. A rug pull scam usually relies on privileged functions that let deployers drain a pool, mint unlimited tokens, block sells, or change fees after liquidity arrives. Users deposit because the UI looks clean and the APY looks tempting, then the exit door locks.
This risk is higher in new tokens, new farms, and copy-paste contracts. It also shows up in NFT mints, where the mint page asks you to sign something that gives broad rights. You reduce this risk by checking who controls admin keys, whether the code is verified, whether the team has a track record, and whether reputable communities have stress-tested the project.
Unlimited Token Approvals (The Silent Threat)
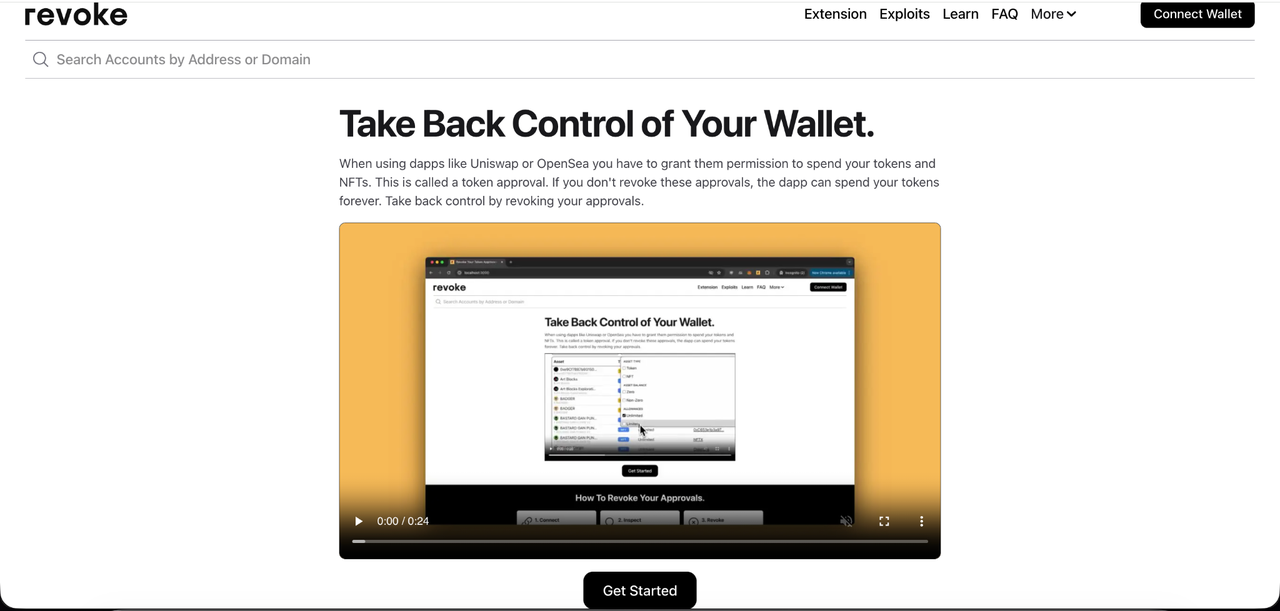
When you swap on a DEX or use a lending protocol, you usually approve a contract to spend your tokens. That is how the contract can move your USDC,ETH, or NFTs on your behalf. Revoke.cash explains token approvals as permissions that let a smart contract spend your tokens for you, and it also explains that NFT approvals can be limited to a single token or unlimited for a whole collection.
The convenience trap is unlimited approvals. Many apps ask for unlimited approval so you can trade again without repeating the approval transaction. If that contract gets exploited later, a thief can use the existing approval to drain that token from your wallet, even if you are not on the site.
Revoke.cash even tracks approval-related exploits where attackers abuse approvals to steal funds outside the exploited contract’s own balance. Wallet drainers also lean on these permissions, and Trust Wallet warned in 2025 that lingering approvals can expose you to unauthorized access.
Your Security Checklist: How to Protect Yourself
You cannot remove all risk in DeFi. You can remove the easy wins attackers love. The checklist below focuses on actions you can repeat, so you do not rely on memory when you are tired, excited, or rushing. This is the practical side of DeFi security and how to avoid crypto scams without turning into a full-time investigator.
DYOR (Do Your Own Research)
Start with the basics that scammers cannot fake easily. Check whether the team is public and whether they have shipped anything before. Anonymous teams can be legitimate, but you should treat them as higher risk by default.
Then look at the community. Real projects have disagreement, bug reports, and support threads. If you only see good feedback and referral codes, step back. Also check whether the docs match the product. Thin docs and thick marketing is a common red flag.
Check for Audits
A smart contract audit is a third-party review where a security firm inspects code, tests common exploit paths, and documents findings. Audits help, but they do not guarantee safety. Attackers also target front-ends, admin keys, and users.
The Trail of Bits Blog put the real problem bluntly in a 2025 security post:
"design protocols that can safely tolerate private key compromise"
As a user, read audits like you read a home inspection report. Look for scope, commit hash or version, severity of findings, and whether the team fixed issues with a follow-up review. If the site says audited but provides no report, treat that as not audited.
Use a Burner Wallet
Separate your funds by purpose. Keep a main wallet for long-term holdings and a second wallet for new dApps, mints, and experiments.
The numbers back this up. CertiK’s H1 2025 report said wallet compromise was the most costly attack vector, with about $1.71B stolen across 34 incidents, and phishing was next with about $410.7M stolen across 132 incidents.
Even large players can fall to signing tricks. In its technical analysis of the Bybit incident, CertiK described a phishing attack that deceived wallet signers into signing malicious transaction data, leading to a contract upgrade that enabled the drain.
Revoke Your Approvals
Approvals are not a one-time decision. They are ongoing permissions, and you should review them like you review app permissions on your phone.
Revoke.cash provides an approval checker and a simple process: connect or enter your address, inspect approvals, and revoke the ones you do not use. When you revoke, your wallet signs a transaction, and you pay a small gas fee.
A practical routine works well for most people:
- Revoke approvals after you stop using a dApp.
- Revoke the unlimited approvals you granted months ago.
- Review NFT approvals after any minting spree, since marketplaces often use broad approvals.
If It Looks Too Good to Be True, It Is
Extreme APYs often exist to pull in deposits fast. Sometimes the project collapses because the token emissions are unsustainable. Other times, it is outright theft.
Tie this back to the broader threat landscape. Chainalysis described 2025 as a high-loss year with more than $3.4B stolen, and TRM Labs said 2025 losses were highly concentrated with a single mega-incident driving a large share of theft. When attackers earn billions, copycats appear.
Conclusion: Be Paranoid, Be Protected
You cannot outsource safety on-chain. You can reduce your risk a lot with a few habits, such as researching before you deposit, preferring audited code with clear reports, using a burner wallet, and revoking approvals regularly.
Smart contract security works best when you treat it as a routine, not a one-time setup. If you trade on exchanges like Bitunix, you operate in a more centralized environment with different protections. When you go on-chain, use the checklist above so your curiosity does not turn into a donation.
At Bitunix, we operate in a secure, centralized environment to protect you from the inherent risks of the decentralized world. For your on-chain adventures, use the strategies in this guide to stay safe. For your trading needs, download the official app,create an account, and trust the proven security of the Bitunix platform.
FAQ Section
What is a smart contract audit?
A smart contract audit is a structured security review of code by a third-party firm. The auditors look for bugs, unsafe permissions, and exploit patterns. A good audit report includes scope, findings, severity, and recommended fixes, plus evidence that the team addressed the issues.
If a project is audited, does that mean it is 100% safe?
No. An audit checks a specific version of code for known issues, but it can miss unknown bugs, economic attacks, or oracle failures. Teams can update contracts after the audit, and private keys or admins can be compromised. Audited projects have still been hacked later.
What is a honeypot scam?
A honeypot scam is a token or dApp built so that buying looks normal, but selling or transferring is blocked by contract rules. Victims get trapped holding worthless tokens while the creator can exit or drain liquidity.
How can I tell if a team is anonymous?
Check whether founders, developers, or advisors use real identities across multiple platforms, and whether reputable partners vouch for them. Anonymous teams can still be real, but you should demand stronger evidence like public audits, verified code, long uptime, and transparent governance.
Is it safe to connect my wallet to a website?
It is safe only when you control what you sign. Connecting alone does not move funds, but approvals and signatures can. Always verify the domain, avoid links from DMs, and read approval prompts. Use a burner wallet for new sites and revoke permissions later.
What is Revoke.cash, and is it safe to use?
Revoke.cash is a tool that lets you view and revoke token approvals across many networks. It works by prompting your wallet to submit an on-chain revoke transaction. You still sign in your wallet, so you control execution. Revoking costs gas, like any transaction.
What is a phishing attack?
Phishing is tricking you into revealing secrets or signing harmful transactions. In crypto, phishing often targets seed phrases, fake support chats, and signature requests that look routine.
Does using a hardware wallet protect me from smart contract risk?
A hardware wallet helps protect private keys, but it does not stop you from approving a malicious contract. If you sign an unlimited approval or a bad transaction, the hardware wallet still executes your intent. Combine hardware wallets with approval hygiene and a burner wallet strategy.
What should I do if I think I interacted with a malicious contract?
Move remaining assets to a fresh wallet, revoke approvals from the compromised address, and stop using that device until you check it for malware. Then review recent transactions and approvals to identify what was granted. Report the scam domain to your wallet provider and community channels.
Where can I learn more about common smart contract exploits?
Learn common smart contract exploits from OWASP Smart Contract Top 10, which ranks real-world risk classes like access control and reentrancy. Use the SWC Registry to study specific weakness patterns and examples. Practice by solving Damn Vulnerable DeFi challenges that simulate attacks in a sandbox.
Glossary
- Approval: Permission that lets a contract spend your tokens without asking again.
- Allowance: The maximum token amount a contract can spend under an approval.
- Block explorer: Website that shows on-chain transactions, contract code, and approvals history.
- Burner wallet: Secondary wallet with limited funds used for risky dApps and mints.
- Cold wallet: Wallet setup designed to keep keys offline and reduce remote theft risk.
- DEX: Decentralized exchange that swaps tokens via smart contracts and liquidity pools.
- Front-end attack: Compromise of a website UI that tricks users into signing bad transactions.
- Immutable contract: Contract that cannot be changed after deployment, even if it has bugs.
- Multisig: Wallet that requires multiple signatures to approve actions, reducing single-key risk.
- Phishing: Social engineering that tricks you into sharing secrets or signing harmful actions.
- Re-entrancy: Bug pattern where repeated calls drain funds before balances update.
- Revocation: On-chain action that sets an allowance to zero and removes contract spending rights.
- Rug pull: Malicious exit where creators drain liquidity or trap users after deposits arrive.
- Smart contract: Program on a blockchain that executes rules for swaps, lending, and transfers.
- Upgrade mechanism: Design that allows code changes after deployment, controlled by admins or governance.
About Bitunix
Bitunix is a global cryptocurrency derivatives exchange trusted by over 3 million users across more than 100 countries. The platform is committed to providing a transparent, compliant, and secure trading environment for every user. Bitunix offers a fast registration process and a user-friendly verification system supported by mandatory KYC to ensure safety and compliance. With global standards of protection through Proof of Reserves (POR) and the Bitunix Care Fund, Bitunix prioritizes user trust and fund security. The K-Line Ultra chart system delivers a seamless trading experience for both beginners and advanced traders, while leverage of up to 200x and deep liquidity make Bitunix one of the most dynamic platforms in the market.
Bitunix Global Accounts
X | Telegram Announcements | Telegram Global | CoinMarketCap | Instagram | Facebook | LinkedIn | Reddit | Medium
Disclaimer: Trading digital assets involves risk and may result in the loss of capital. Always do your own research. Terms, conditions, and regional restrictions may apply.